MIPI Camera Security Framework
Providing end-to-end security to applications that leverage MIPI specifications

Developed by: Security Working Group
A framework to protect automotive CSI-2 data streams and associated command and control channels
Industries
Sign Up for the Security Mailing List
Stay up to date with new specifications and activities related to the MIPI Camera Security framework.
Overview
The MIPI Camera Security Framework defines a flexible approach to add end-to-end security to automotive image sensor applications that leverage the MIPI CSI-2 specification. The framework enables key security functionality, including authentication of image system components, data integrity protection and data encryption, and protection of image sensor command and control channels. It provides implementers with a choice of protocols, cryptographic algorithms, integrity tag modes and security protection levels. The framework is uniquely effective in both its security extent and implementation flexibility.
The initial release of the camera security framework focuses on securing long-reach, wired in-vehicle network connections between MIPI CSI-2®-based image sensors and their related processing ECUs. While acknowledging this initial focus, the framework may also be applicable to other non-automotive machine vision applications that leverage MIPI CSI-2-based image sensors.
The framework consists of the following specifications:
- MIPI Camera Service Extensions (MIPI CSE) v2.0 – a companion specification to MIPI CSI-2, defines security services to enable data integrity protection and optional encryption of CSI-2 data. This is in addition to the functional safety services provided in CSE v1.0.
- MIPI Camera Security v1.0 – defines system security management of MIPI CSE and MIPI CCISE, using the DMTF (Distributed Management Task Force) SPDM (Security Protocol and Data Model) architecture to authenticate and establish secure sessions between imaging system components.
- MIPI Camera Security Profiles v1.0 – defines a set of common security profiles for the MIPI Camera Security Framework to enable interoperability, including profiling SPDM authentication mechanisms.
- MIPI Command and Control Interface Service Extensions (MIPI CCISE) v1.0 – an additional companion specification to MIPI CSI-2, defines security services to enable data integrity protection and optional encryption of the MIPI Command and Control (CCI) interface based on I2C.
The framework is described in the white paper, "A Guide to the MIPI Camera Security Framework for Automotive Applications."
The camera security framework has been developed by the Security Working Group in collaboration with the Camera Working Group.
Protecting Automotive CSI-2 Image Data from Cybersecurity Risks
Automotive image sensors, which include cameras, lidars, radars and other sensors, are essential to the latest advanced driver-assistance systems (ADAS) and autonomous driving systems (ADS). Both the number and significance of these image sensors being deployed in these safety-critical applications will continue to increase with each new generation of automotive architecture, and MIPI CSI-2 has quickly become the de facto image sensor interface within these systems.
Within this context, automotive system designers understand the need to protect image sensor data from security risks such as installation of illegitimate substandard components, malicious manipulation of sensor data and potential privacy violations from unauthorized access to location-revealing images. To mitigate these threats, MIPI has developed a camera security framework that protects MIPI CSI-2 image data (and any associated command and control data) “end-to-end” between image sensor components and their related electronic control units (ECUs). As described in more detail below, the framework is uniquely effective in both its security extent and implementation flexibility.
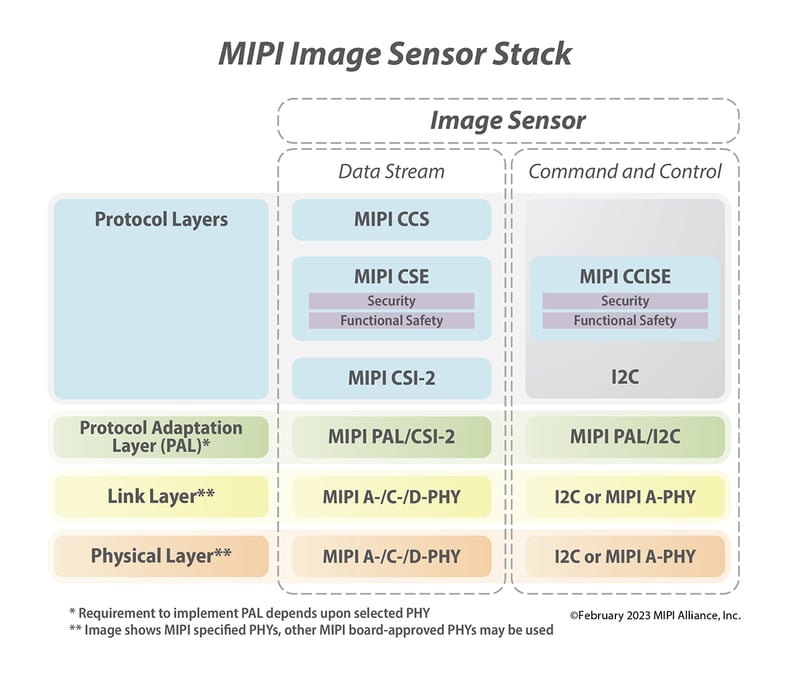
Figure 1. MIPI image sensor stack incorporating the Camera Security Framework
End-to-End Security Extent
Whereas other image sensor security methods protect the link layer, the MIPI Camera Security Framework delivers application-level protection across all physical attack points. In this way, it is “end-to-end,” or “silicon to silicon,” in that the security transcends all link layer components to provide security from the source of sensor data in sensor silicon to the ultimate sink of that data in system-on-chip (SoC) silicon. Security is applied to both data streams, and command and control data.
Further, this end-to-end protection is guaranteed irrespective of the underlying communication network topology (e.g., unicast, multicast, daisy-chain topology), providing complete flexibility for the developer to leverage any combination of underlying network components (such as bridges, aggregators and forwarding elements) to achieve the most efficient solution for their application.
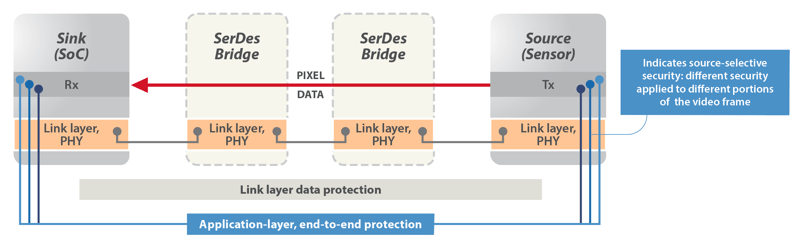
Figure 2. The MIPI Security Framework provides both end-to-end security extent and a high degree of implementation flexibility.
High Scalability Provides Implementation Flexibility
The MIPI Camera Security Framework is highly scalable, providing a high degree of implementation flexibility for sensor application developers to balance required security levels against processing efficiency, implementation complexity, thermal regulation and/or power consumption in the sensor system. The framework provides this flexibility in four primary ways:
- Choice of service protocol. The framework allows the implementer to choose between two data service protocols for the desired security level. It is these protocols that embed the necessary Message Authentication Code (MAC) for integrity protection into a CSI-2 data stream. The two data service protocols are called Service Extensions Packet (SEP) and Frame-Based Service Extensions Data (FSED). SEP-based security is provided by adding SEP headers and footers to each CSI-2 packet (or frame), whereas FSED security is provided via the addition of (up to) three additional CSI-2-based packets to an image frame. Both protocols can be implemented with a high level of commonality to enable dual-protocol implementations if required.
- Choice of ciphersuites. The framework defines two ciphersuites, one for efficiency and one for performance. The "efficiency" ciphersuite provides AES-CMAC data integrity only (no encryption) and is targeted toward sensors with limited hardware resources. The "performance" ciphersuite provides AES-GMAC data integrity and optional AES-CTR encryption and is targeted at sensors with dedicated hardware support for these security protocols.
- Choice of integrity tag modes. The framework offers multiple tag mode options when using the SEP and FSED data service protocols. This allows the implementer to choose how often the tag is computed and transmitted. For example, when using SEP, the implementer has the choice to send the Message Authentication Code (MAC) tag on a per-message, per-data-type or per-frame basis.
- Highly granular security controls. A new security paradigm provides highly granular security controls over the different segments of the CSI-2 image frame to enable a “sliding scale” of security levels to be implemented. This scale includes: at the highest security level, applying full data integrity and encryption to the whole image frame; to partial security levels, where source selective integrity protection is applied to a subset of data within an image frame; to applying no data integrity at the lowest security level. The level of security is configurable on a frame-by-frame basis with camera stream data being augmented with packets/messages containing the relevant security information.
Supporting MIPI Automotive SerDes Solutions (MASS)
The MIPI Security Framework is a key component of MIPI Automotive SerDes Solutions (MASS), an end-to-end, full stack of connectivity solutions for the growing number of cameras, sensors and displays that enable automotive applications. The framework complements the MASS image sensor "stack" by adding security into both the Camera Service Extensions layer and Command and Control Interface.
It should be noted that the camera security services defined within the security framework are fully complementary to the camera functional safety services already provided within MASS.
Additional Information
The October 2024 white paper, "A Guide to the MIPI Camera Security Framework for Automotive Applications" takes a more detailed look at how the framework delivers application-layer security for end-to-end data protection, and configurable security levels based on application requirements.
The MIPI CSI-2 Security Forum, presented in January 2023 by the co-chairs of the MIPI Security Working Group, provided a comprehensive introduction to the MIPI Security Framework, the framework’s security objectives and its underlying components. Learn more on the MIPI blog and view the forum on demand.
Security Mailing List
For updates on MIPI security specifications, upcoming events and new security resources, sign up for the security mailing list.